Session Hijacking Tutorial
October 29th, 2010 Posted in Hacking, Security, Tutorial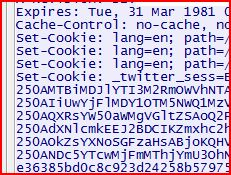
Recently, there has been a lot of talk about the Firesheep plugin for Mozilla Firefox that allows users to easily perform a session hijacking against victims on the same LAN. The news spread fast and wide, and reporters were deeming Firesheep extremely dangerous. I am not going to play down the fact that this does pose a serious threat to people’s privacy; however, this is nothing more than an old trick with a new face. Session hijacking has been around for ages, and performing a session hijack is actually quite simple. Today I will demonstrate one way to perform a simple session hijack without Firesheep!
What is Session Hijacking?
I am not going to waste time trying to explain session hijacking; instead I will just give you a blurb from Wikipedia:
In computer science, session hijacking refers to the exploitation of a valid computer session—sometimes also called a session key—to gain unauthorized access to information or services in a computer system. In particular, it is used to refer to the theft of a magic cookie used to authenticate a user to a remote server. It has particular relevance to web developers, as the HTTP cookies used to maintain a session on many web sites can be easily stolen by an attacker using an intermediary computer or with access to the saved cookies on the victim’s computer (see HTTP cookie theft).
How to Perform a Session Hijack
For this simple example using Windows, I am going to target Twitter (as this seems to be one of the two big targets of Firesheep, and since I refuse to use Facebook). Here are the following things that will be needed for this example:
- LAN with Internet connection.
- Two computers (technically you could just use one, but it’s more fun to see it work with two).
- Wireshark
- Mozilla Firefox
- Add N’ Edit Cookie Editor add-on (or another cookie editor of your choice)
The first step I am going to take is to start Wireshark and sniffing traffic. Depending on the LAN you may need to perform ARP Spoofing to successfully pull this attack off; if you need to know how to perform an ARP Spoofing attack I would suggest search Google or drop me a line (webmaster[at]veritablelife.com or @aaronbeauregard) and I will help you out.
While sniffing traffic, log into Twitter on the other computer. After you have logged into Twitter, you can stop sniffing traffic and perform a find packet (Ctrl-F or Edit–>Find Packet). For the criteria, set the “By:” option to “String” and the “Search In” option to “Packet details”, and search for “Set-Cookie:” in the text field.
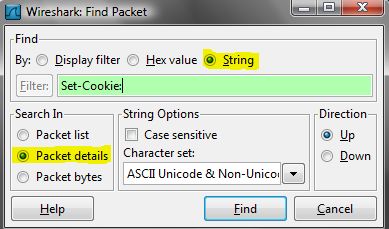
Find Packet options
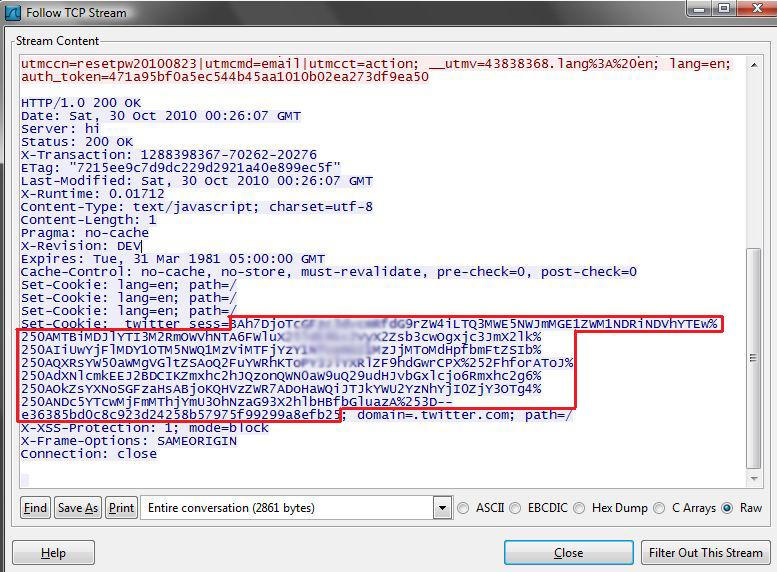
Once you search, a packet, with the word Set-Cookie, will be highlighted; right-click the packet and select “Follow TCP Stream.” This will make it easier to read, when looking at the TCP Stream you will see “Set-Cookie: _twitter_sess=” and then a long string of characters. This is the session cookie that you are going to hijack.
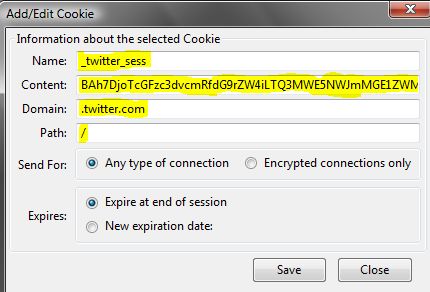
Since we now have the cookie, open Mozilla Firefox and open our Cookie Editor (Tools –> Cookie Editor). Once the Cookie Editor is open, select the Add button under Cookie. For the parameters enter the following:
- Name: _twitter_sess
- Content: copy paste the information from the TCP Stream (see the red box in the Session Cookie Found from TCP Stream picture)
- Domain: .twitter.com
- Path: /
After all this information is entered, save the cookie. The next step is to go to the address bar and go to Twitter.com, and just like that you have hijacked another users’ session.
Quick and Dirty Instructions:
- Sniff traffic
- Log into Twitter with another computer (or same computer)
- Stop sniffing traffic
- Find a packet that contains Set-Cookie
- Open Firefox
- Start Cookie Editor add-on
- Paste in cookie
- Go to Twitter
- No need to log in!!
Conclusion
As stated earlier this was a simple example; but as you can see, the same steps can be applied to hijack sessions from other websites. I will give credit to Firesheep, as it made this very easy process even easier and has even made people more aware of the dangers of surfing the web on public networks.
6 Responses to “Session Hijacking Tutorial”
By Anurag Sharma on Feb 22, 2015
thanks
By Sundher on Oct 24, 2015
Thank you very much for posting salesforce online training.You can search and visit our website.with best regards:
salesforce online training
By hadoop online training on Aug 29, 2016
Nice and thanks for sharing the informative data hadoop online training
By lolnexus on Oct 19, 2017
Valuable information! Looking forward to seeing your notes posted. The information you have posted is very useful. Keep going on, good stuff. Thank you for this valuable information.
By lolnexus on Oct 19, 2017
Valuable information! Looking forward to seeing your notes posted. The information you have posted is very useful. Keep going on, good stuff. Thank you for this valuable information
By adbfire on Jan 7, 2018
I’m very happy to find this page. I need to to thank you for your time due to this fantastic read!! I definitely enjoyed every part of it and I have you book marked to see new stuff on your web site.